
Cryptocurrency exchange operator Coinbase has revealed it responded to an incident in early February where an employee had their credentials compromised, but thankfully resisted an attempt by the attacker to socially engineer their way past the MFA protections they had in place.
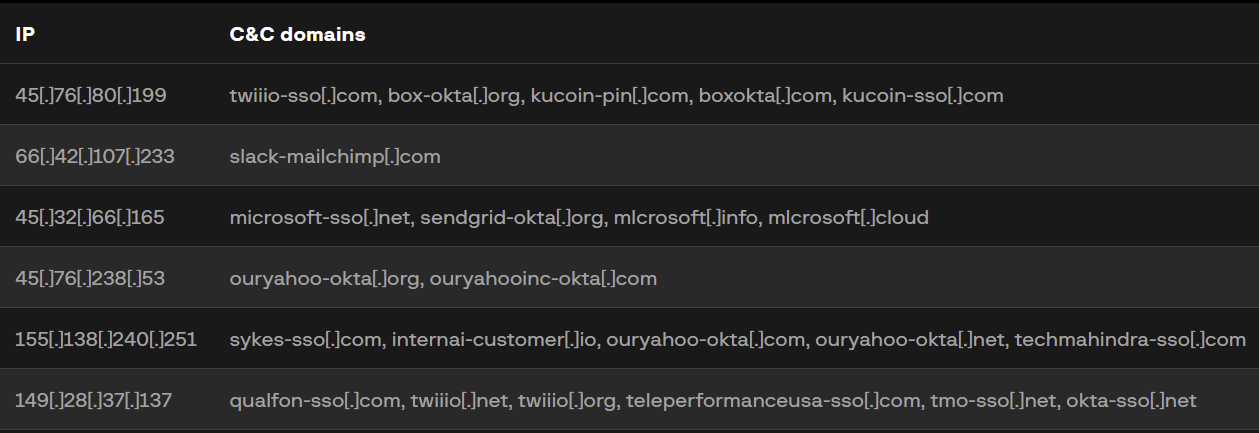
Coinbase have pointed to technical overlaps with the 0ktapus campaign which took place last year and appeared to target customers of the identity provider Okta. Nearly 10,000 accounts in over 130 organisations were compromised through the campaign, which included techniques eerily similar to what was employed in this attack.

Significant Overlap in TTPs
The 0ktapus campaign marked the beginning of activity attributed to a new threat group that is now tracked as UNC3944 (Mandiant) or Scattered Spider (CrowdStrike).
While their activity has since been reported on mainly due to their experimentation with the bring-your-own-vulnerable-driver (BYOVD) technique and abuse of the Windows Hardware Compatibility Program, the attempted attack on Coinbase marks a return to their tried and true TTPs that earned them their current notoreity.
SMS Phishing
The 2022 attack on cloud service provider Twilio – as with many other victims – began with malicious links being delivered via SMS, direct to employees:
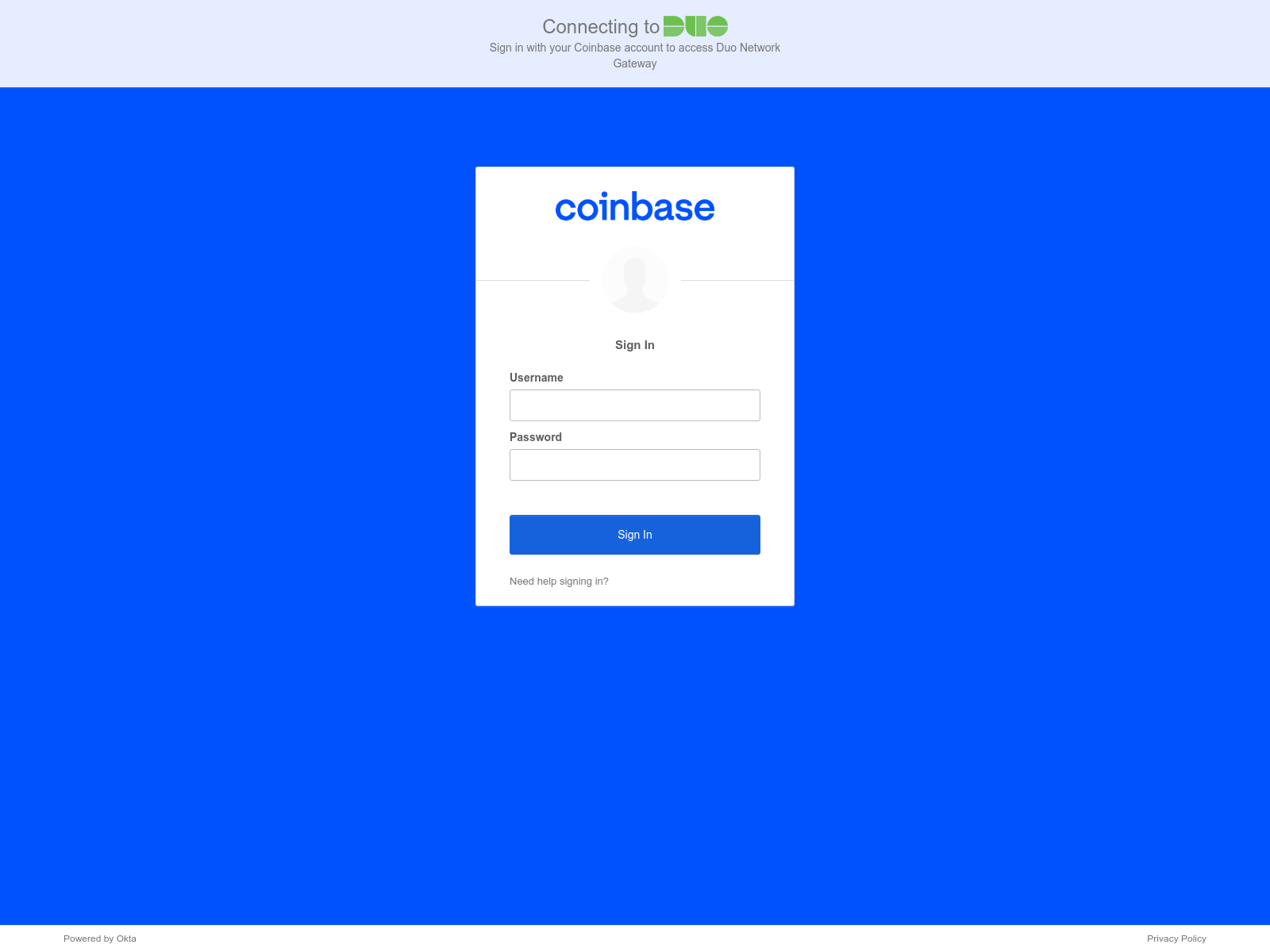
The links redirected to a spoofed sign-in page for Twilio employees – exactly the same as appears to have occurred in the attack on Coinbase:
SMS Phishing is particularly useful as – when delivered to the phone of an employee which isn’t enrolled in or protected by a Mobile Device Management (MDM) solution – it circumvents traditional Phishing mitigations in place on corporate networks.
Bypassing MFA
UNC3944 were noted to have directly called employees to understand the organisation’s Authentication flow and spammed them with MFA prompts (MFA Fatigue) in an attempt to circumvent MFA protections during the 0ktapus campaign. Moreover, Group-IB found that at least 5,441 MFA codes were stolen throughout their long-running campaign.
In this instance, they opted to attempt to socially engineer the Coinbase employee into helping them bypass MFA by calling them and purporting to be a member of the IT team, after having earlier stolen their credentials via the SMS Phishing lure.
On this, Coinbase have recommended being wary of incoming phone calls or text messages from the following providers:
- Google Voice
- Skype
- Vonage/Nexmo
- Bandwidth[.]com
Use of lookalike domains
Coinbase also warned that the actors behind the attack might register and use domains which resemble the company’s trusted services such as sso-<companyName>.com or login.<companyName>-sso.com.
The screenshot of the spoofed Coinbase login page we shared above, for example, was served up via the domain sso-cb[.]com.
This exact technique was used extensively during the 0ktapus campaign, and was adapted to match either the organisation being targeted or the provider they were attempting to masquerade as.
Additional Takeaways
Coinbase have generously shared a list of specific TTPs that stood out from this attack. The full list can be found in their disclosure, but at a high level and in addition to what’s mentioned above, Defenders should watch out for:
- Unauthorised, successful/attempted downloads of the AnyDesk (anydesk[.]com) or ISL Online (islonline[.]com) remote desktop viewing software;
- Attempts to access the organisation from a 3rd-party VPN provider, specifically Mullvad VPN – which was similarly called out by Okta as a constant within the 0ktapus campaign of 2022;
- Unexpected attempts to install the EditThisCookie browser extension;
- Use of unapproved text/file-sharing services such as riseup[.]net;
- Attempts to enumerate customer support or employee directory applications.
Growing sophistication
UNC3944 is a highly capable threat group which has continued to experiment with new techniques in the past year, in an expansion of the tradecraft which proved so successful in the 0ktapus campaign of 2022.
The combination of their demonstrated skill – not just in circumventing MFA protections to gain initial access, but through leveraging signed and vulnerable drivers to evade EDRs – makes them a threat that all organisations should take note of and prepare to defend against.
Appendix A: Mitigating MFA Bypasses
This attack has reinforced how simple phone-based social engineering is used to coerce users into approving MFA prompts; and while MFA fatigue wasn’t applied in this instance – it’s a known part of UNC3944’s toolkit, and has worked in the past to compromise the likes of Cisco, Microsoft, and Uber.
In preparation for this threat, here are a few suggestions on how to mitigate it:
- Enable number matching for Azure AD MFA prompts, and give them context on where the login attempt is coming from so they can judge if it’s a dropped VPN trying to re-authenticate, or a hacker in Argentina trying to mess with them. These measures, combined, can help mitigate MFA fatigue and social engineering attempts;
- Implement layered Conditional Access Policies, in addition to MFA. E.g. user must be on an MDM-enrolled device with EDR installed; connected to the corporate VPN, and have approved a number-matching MFA prompt to authenticate;
- Use physical FIDO tokens as your MFA factor – remote attackers can’t easily spoof or socially-engineer this, so they’re much more resilient than both soft and hard tokens;
- Reduce session-token validity to 24-hours to minimise the time an attacker can maintain access before needing to again bypass MFA;
- Anticipate compromise – closely monitor Privileged Accounts to compensate for gaps in policy or visibility. Prevention is always ideal, but never a sure thing. Make sure you’re set-up to detect anomalous and unapproved activity by privileged accounts.
Leave a Reply