
***** Start Executive Tearline *****
Cyber criminals will consistently seek out the path of least resistance when searching for victims to attack. Unfortunately for Australia, it has served as the proverbial lighting rod for the latest strikes that have resulted in data theft and extortion attacks against our second largest Telco, Optus; our largest private health insurer, Medibank, and more.
This is part of a larger trend, with one cyber security vendor reporting an 81% increase in attacks on Australian organisations in the 11 months to June 2022, and another finding there was a 56% increase in ransomware attacks targeting entities in Asia over the first three quarters of 2022.
Australian legislators are responding by calling for increased financial penalties and scrutiny for companies that suffer serious data breaches, which builds on a two-part Bill targeting critical infrastructure operators that passed into law earlier this year.
Prepare for a changing regulatory environment, greater oversight
Australia has already significantly bolstered critical infrastructure protections through passing the Security Legislative Amendment (Critical Infrastructure Protection) Bill 2022 (a.k.a. the SLACI Act), and is attempting to achieve a similar outcome for personal data with the Privacy Legislation Amendment (Enforcement and Other Measures) Bill 2022, which was introduced into Parliament on the 26th of October.
If passed, this bill will:
Significantly increase the potential penalty for “serious or repeated privacy breaches”;
Provide the Office of the Australian Information Commissioner (OAIC) with powers to:
Request information and conduct compliance assessments of the notifiable data breach regime;
Require entities to conduct external reviews of their internal processes and to notify affected individuals of specific privacy breaches;
Establish information sharing powers for the OAIC and Australian Communications and Media Authority (ACMA).
The government is also taking steps to empower enforcement agencies, announcing in the recent Federal Budget that the OAIC would receive an additional $5.5 million in funding over two years to help it “investigate and respond” to the Optus breach, and a further 48 staff in the next financial year to boost its overall workforce.
As mentioned, all this is in addition to the SLACI Act which applies to organisations operating in 13 critical infrastructure sectors. The Act establishes increased reporting obligations; mandates the adoption of a risk management program, and affords the government step-in powers in the case of a cyber incident impacting an organisation governed by the Act.
A full summary of what this means for affected organisations can be found here.
Recommendations
Organisations operating in a sector governed by the SLACI Act should familiarise themselves with what it means for them and take immediate steps to ensure compliance if you aren’t already, as it is already in force.
Obligations stemming from this Act may be further compounded by measures laid out in the Privacy Legislation Amendment Bill currently before Parliament if it is passed. You can monitor the progress of the Bill by clicking the “Track” button on the official Parliamentary Business page.
Regardless of the outcome, it’s worth noting the key factors that brought the Optus and Medibank breaches into the public spotlight were:
- Their market presence, and subsequently the number of individuals impacted;
- The criticality of the services provided – both Optus and Medibank are captured under the SLACI Act;
- The sensitivity of the stolen data, and its potential to be abused for identity theft and fraud.
Organisations whose business model alligns with the above factors would benefit greatly from proactively evaluating existing data security measures; investing in Data Loss Prevention measures, and establishing Incident Response and Cyber Security Monitoring teams and processes.
***** End Executive Tearline *****
Privacy Matters – How did we get here?
A sudden burst of high-profile breaches this month has cast a spotlight squarely on Australian organisations and government agencies. Specifically, it has raised questions on their ability to both prevent and respond to breaches of their networks and sensitive customer information.
The theft of 9.8 million customer records from Australia’s second-largest Telco, Optus, has been followed swiftly by another data breach impacting Medibank – the largest health insurer in Australia.
Interestingly, in a seven day period in that same week, PII of some 500,000 subscribers to Australian wine retailer Vinomofo were stolen from a test system; online retailer MyDeal suffered a breach of 2.2 million customer records, and energy company EnergyAustralia reported unauthorised access to the accounts of 323 residential and business customers.
Unlike the breaches of Optus and Medibank, these quickly fell out of the news cycle. Why?
At first glance you might think the quantity of breached records for MyDeal or criticality of EnergyAustralia’s systems might warrant more scrutiny or outrage, but what is consistent in these three breaches is the type and sensitivity of data that was stolen.
In the cases of both Medibank and Optus, key identity documents such as drivers license or Medicare details were stolen. A Drivers license alone is sufficient to satisfy regulatory requirements for a bank’s Customer Identification Process, while paired with a Medicare card it will count for 75 of 100 points of ID required for a National Police Check.
The potential for identity theft – and at such a huge scale – clearly delineates the Optus and Medibank breaches from the more commonplace thefts of personal data or credit card information, and has forced the Australian government to take decisive action.
It’s against this backdrop that the Australian Government have introduced a Bill to Parliament which seeks to increase penalties for “serious or repeated privacy breaches” and provide the key privacy watchdog – the Office of the Australian Information Commissioner – more powers to tackle privacy breaches.
This measure comes on the heels of the previous government’s proposed – but not legislated – criminal penalties for ransomware attacks on critical infrastructure, and a landmark two-stage Critical Infrastructure Protection Bill that became law in April this year.
Lessons Learned from Medibank’s Response
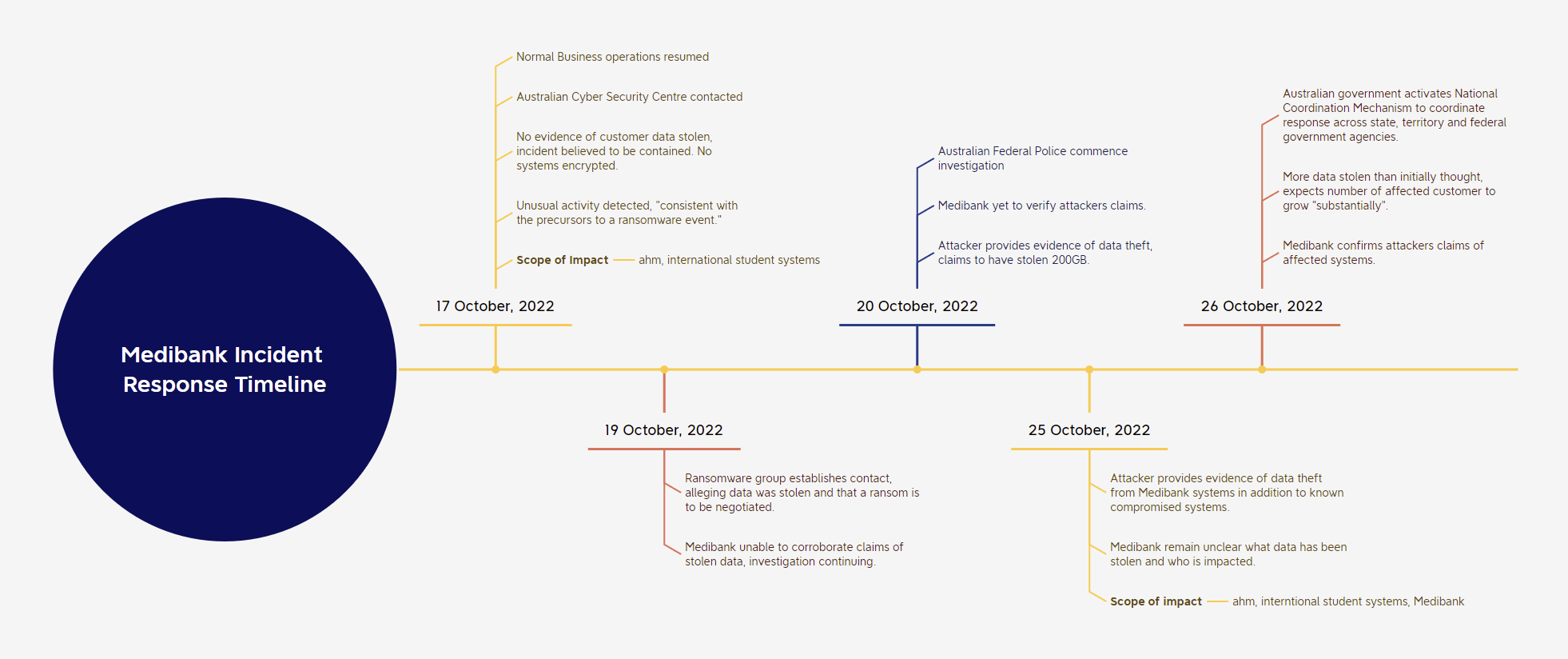
Medibank have struggled from the onset to identify and contain the scope of this breach, with each new discovery appearing to have been revealed by the attacker, and not the investigators themselves.
After initially stating they had intercepted the attack before customer data could be obtained, Medibank quickly backtracked after the attacker contacted them with evidence of customer policies and PII they had stolen, claiming to have exfiltrated 200GB of data in total. The attacker further threatened to find data of prominent customers and “people with very interesting diagnoses” and email it to them in order to further exert pressure on Medibank to negotiate a ransom payment.
The scale of this breach has since grown to further encompass customers of the main Medibank brand, and has to potential to impact a further 3.9 million individuals.
From what we know so far, three key failings can be observed:
- The compromise was not only discovered too late, but mistakenly concluded that the breach was contained without impact to customer data. Investigators failed to uncover evidence of data exfiltration before the actor made contact demanding payment;
- More broadly, there appears to be a lack of network visibility, accesses, and/or immature IR capability and practices, which have hampered their ability – at every step – to adequately gauge the scope of the breach;
- Medibank’s lack of cyber insurance is expected to result in an estimated cost of $25 – $ 35 million to respond to the cyber incident. This represents as much as 23% of their unallocated capital; does not include “further potential customer and other remediation, regulatory or litigation related costs”, and may climb further, the longer the incident drags on and if systems need to be recovered.
It is imperative that organisations and security practitioners heed the lessons learned here, in order to ensure history doesn’t repeat itself.
Increased targeting of Australian entities in 2022
The recent spate of compromises of Australian companies comes on the tail of a period of increased targeting of entities operating not just in Australia, but the broader Asia region.
Cyber security vendor Imperva recently reported they observed an 81% increase in attacks on Australian organisations in 11 months to June 2022. Attacks they rated as “critical” rose 230% between August 2021 and May this year – nearly twice the global rate during the same period.
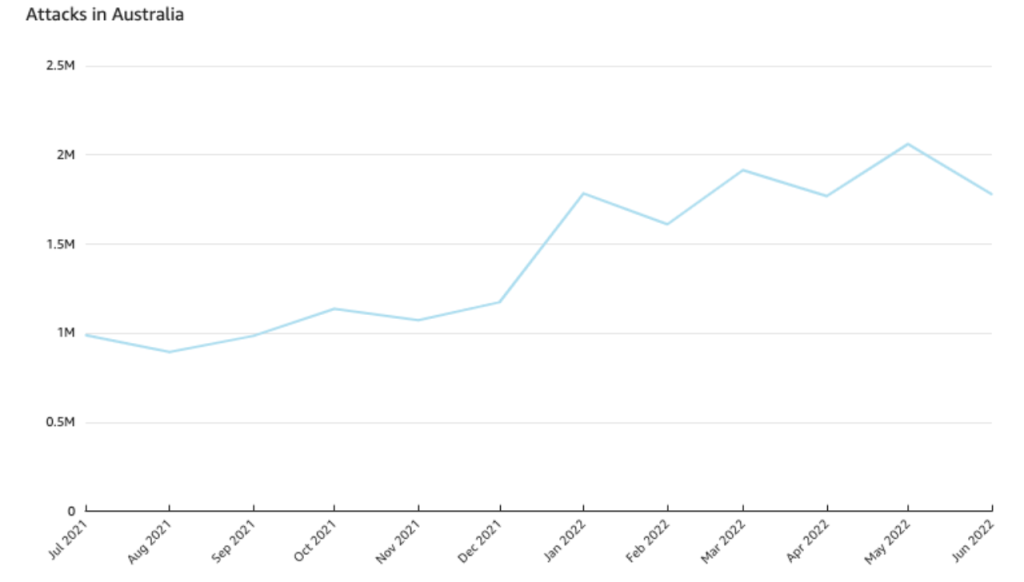
A fellow industry player, Sonicwall, has highlighted a drastic shift in targeting away from the US and UK in preference of Europe and Asia-based targets over the first three quarters of 2022. Organisations in Asia saw a 38% increase in malware delivery, and a staggering 56% increase in ransomware attacks compared to 2021.
Where to from here?
Just this week Microsoft released a report looking at a ransomware actor it tracks as DEV-0832, noting that “the group is financially motivated and continues to focus on organizations where there are weaker security controls and a higher likelihood of compromise and ransom payout.”
This brings us back to my original point from the start of this piece – cyber criminals will consistently seek out the path of least resistance, and so it’s imperative that your organisation nails the basics to avoid being targeted.
The vast majority of cyber incidents stem from one of three attack vectors:
- Compromising vulnerable internet-facing assets – typically resulting from unpatched vulnerabilities;
- Delivering malware via Phishing emails;
- Stolen credentials – these can be purchased trivially on the Dark Web; and according to a “source close to the [Medibank] investigation”, were the root cause of the ongoing breach;
Recommendations: Protect & Detect
Implement Multi-Factor Authentication (MFA) across all user accounts
MFA is your best bet to preventing unauthorised access to internal resources and systems – even if a set of valid user credentials are compromised, an attacker won’t be able to log in without that second factor of authentication.
While highly effective against low-sophistication attacks such as password spraying and credential stuffing, no defence is perfect (demonstrated through the 0ktapus compromises, for example), which is where recommendation #2 comes in:
Enforce granular Conditional Access policies
In addition to requiring an additional authentication factor, major identity providers – such as Microsoft’s Azure Active Directory – provide the ability to configure strict requirements for devices that login attempts originate from.
The specific criteria you can apply depends on the technologies you have, but can include things like:
- Requiring the device to be enrolled in your company MDM (e.g. Microsoft Intune);
- Ensuring the remote asset is fully patched and has an up-to-date antivirus running;
- Restricting the physical location and/or IP address space the authentication event can originate from;
- Preventing authentication from devices not connected to the company VPN.
Implement/plan for adoption of FIDO Keys
While soft tokens such as SMS or App-based offerings are low-cost and relatively straightforward to implement, FIDO keys (e.g. the Yubikey) can be used as a physical token in the MFA authentication flow. This makes abusing stolen credentials virtually impossible for remote attackers, as they aren’t able to steal physical tokens in the same way they can soft tokens, in order to bypass MFA.
🔑How does a FIDO security key limit the hacks we’re seeing in the news now?🔑
Beyond fun to work with @Yubico & partner with @Twitter to answer that question + demo how social engineering is used to steal passwords & siphon out MFA codes to gain admin access with @evantobac. — Rachel Tobac (@RachelTobac) 5:19 PM ∙ Sep 28, 2022
While initially highly effective, attackers have adapted to bypass soft token-enabled MFA protections, with services such as the EvilProxy (a.k.a. Moloch) Phishing-as-a-Service platform being sold on Dark Web forums for as little as $400 per month, and able to programmatically bypass both Google and Microsoft’s SMS and Mobile App-enabled MFA.
The impact of this approach was seen at scale in the ScatterSwine/0ktapus compromises, with over 130 organisations compromised through a series of attacks that abused stolen user credentials and intercepted MFA codes to access their internal networks and data.

Microsoft have shared detailed guidance on how to implement stringent MFA and Conditional Access Policies in order to protect against attempts to socially engineer MFA approval, and have recently released an update to their Authenticator app to introduce number matching and provide additional context to MFA requests.
Monitor for PUPs, in particular Remote Management Software
Potentially Unwanted Programs (PUPs) are a challenge for every organisation, though special attention should be paid to Remote Management Software such as AnyDesk, Teamviewer, and Atera.
While predominantly used for legitimate purposes, these tools have been abused by cyber crime and ransomware actors who install attacker-controlled copies of the software in order to gain and maintain access to victim networks.
This research from Synacktiv is an excellent resource for Defenders looking to better understand and detect these tools on your networks.
Monitor for insider threats & unusual user activity
Attackers can’t do much without compromising an identity with the right permissions and accesses – this makes monitoring for uncharacterstic user behaviour an essential measure that can help identify potential compromise. As a minimum, Defenders should look to identify and investigate anomalous login activity and attempts to access resources outside of their business area or remit.
Trusted insiders are one of the most difficult initial access vectors to identify, due to the legitimacy of the recruited insider and their pre-existing knowledge of the network. The Lockbit ransomware crew attempted in August last year to recruit insiders with the promise of multi-million dollar payouts, and the Lapsus$ threat group are known to have paid employees for credentials and MFA approval as part of their wide-ranging hacking spree that hit Microsoft, NVIDIA, Samsung, and more.
Implementing User Behavioural Analytics and Data Loss Prevention solutions can help identify potential Insider Threats, though a good low-cost starting point is to selectively deploy Canary Tokens in your most sensitive network locations and files.

Leave a Reply