Daily News Update: Saturday, April 5, 2025 (Australia/Melbourne)
Australian Super (Pension) Funds targeted in successful Credential Stuffing attack draining member funds. Trump fires NSA/CyberCom Director and NSA Deputy Director over loyalty fears. Incident Response is a race - because it has to be. CVSS 10 RCE vuln in Apache Parquet disclosed, patch now!



Australian Super Funds Targeted in Credential Stuffing Campaign

Multiple Australian superannuation funds (pension funds, to our American friends) have been hit by a significant wave of cyberattacks, primarily identified as credential stuffing, over the weekend of March 29-30, 2025.
The Association of Superannuation Funds of Australia (ASFA) confirmed the attacks, stating that while most attempts were blocked, "a number of members were affected." Reports suggest attackers used stolen credentials, likely obtained from previous breaches and sold online, to gain unauthorised access to members' online accounts via web portals and mobile apps.
Several major funds have acknowledged being targeted:
- Australian Super: Confirmed attackers used stolen passwords to access around 600 member accounts. Chief Member Officer Rose Kerlin stated immediate action was taken to lock accounts. The Guardian reported AU$500,000 ($305,000) was stolen from four Australian Super members. The fund manages over AU$365 billion for 3.5 million members.
- Rest: Became aware of unauthorised activity on its MemberAccess portal. Approximately 8,000 members may have had limited personal details (first name, email, member ID) accessed. Rest stated no funds were transferred out due to these attempts.
- Hostplus: Confirmed members lost no funds but investigations into the impact are ongoing.
- Insignia Financial: Its Expand Platform was hit by credential stuffing, compromising around 100 customer accounts on the Expand Wrap Platform. No financial impact has been found so far. Liz McCarthy, CEO of MLC Expand, urged customers to use unique, strong passphrases and avoid credential reuse.
- Australian Retirement Trust was also mentioned as being affected.
- HESTA and Mercer Super reported they were not affected.
Reuters cited a source claiming over 20,000 accounts were breached across the industry, with some members losing savings. The attacks often occurred during early morning hours, potentially to bypass SMS authentication prompts while users were asleep.
ASFA has established a hotline and released a toolkit to coordinate the industry response via its Financial Crime Protection Initiative (FCPI). Prime Minister Anthony Albanese acknowledged the attacks, noting the government was assessing the situation and that cyberattacks are a frequent occurrence in Australia.
The Register | "Retirement funds reportedly raided after unexplained portal probes and data theft"
The Record | "Cybercriminals are trying to loot Australian pension accounts in new campaign"
Bleeping Computer | "Australian pension funds hit by wave of credential stuffing attacks"
Shake-up at the Top: Haugh Fired from NSA/Cyber Command Leadership
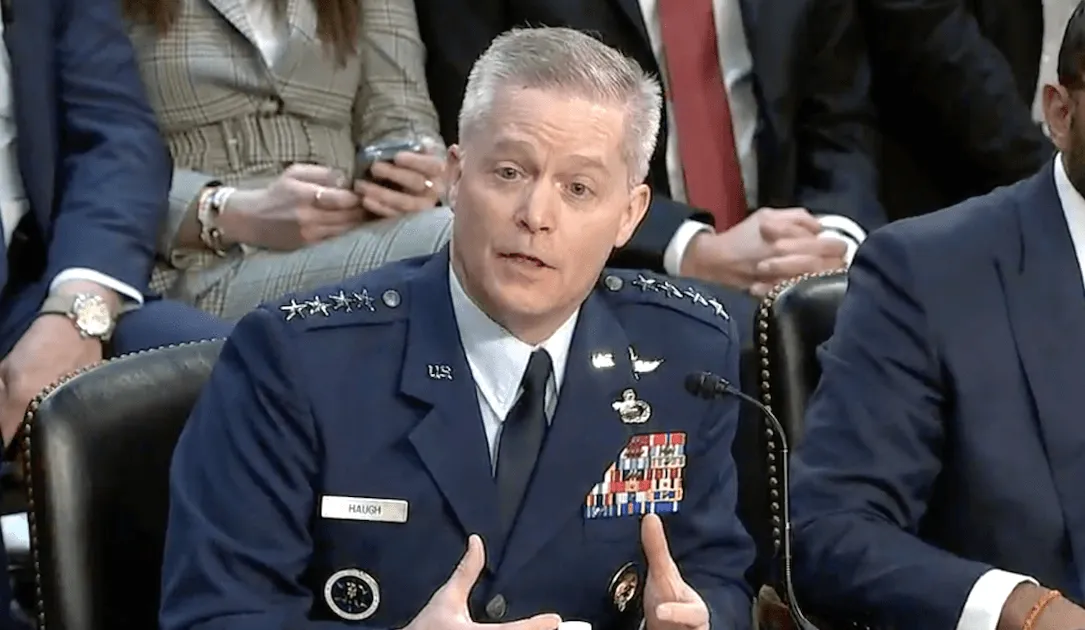
The shakeups and gutting of America's Public Service continues, with President Donald Trump firing Air Force General Timothy Haugh from his dual leadership role as Director of the National Security Agency (NSA) and Commander of U.S. Cyber Command (USCYBERCOM). Haugh had been in the position for just over a year of what is typically a three-year term.
Wendy Noble, the NSA's Deputy Director appointed in 2023, has reportedly also been transferred to a different post within the Pentagon. Haugh and Noble are being replaced by Air Force Lt. Gen. William Hartman - previously the Deputy Commander at Cyber Command, and Sheila Thomas - NSA’s executive director.
The exact reasons for the dismissals remain unclear, though there is strong speculation there's a correlation with a visit by far-right political activist Laura Loomer, who met with President Trump and urged the removal of officials perceived as disloyal. The speculation appears well founded, as Loomer claimed on social media that Haugh and Noble were fired for being "disloyal".
The move has drawn criticism from lawmakers who have questioned the reasoning behind the decision, and how firing Haugh enhances national security, especially given ongoing threats like the 'Salt Typhoon' cyberattacks attributed to China.
Haugh's removal comes as Cyber Command was undergoing a strategic review known as "Cybercom 2.0". It also fuels speculation about the potential separation of the "dual-hat" leadership structure governing the NSA and Cyber Command, a move Trump considered during his first term and was expected to revisit.
All signs point to Trump - once again - taking the lead from external influences, and being easily manipulated into removing anyone who isn't "loyal" to him.
As if the dismantling of the Cyber Security Review Board (CSRB); alleged instruction to US Cyber Agencies to stand down on Russian targets, and blanket cuts to staff across CISA, NSA, and other critical Cyber Security Agencies weren't enough.
The Record | "Haugh fired from leadership of NSA, Cyber Command"
CyberScoop | "Trump fires Gen. Timothy Haugh from leadership of Cyber Command and NSA"
The Register | "Trump fires NSA boss, deputy"
Incident Response Speed vs. Backups: A Recovery Dilemma

While robust backups are fundamental to cyber recovery, a recent discussion highlights the critical, perhaps sometimes overlooked, importance of rapid incident response (IR). The speed at which a threat is detected and contained can significantly impact recovery time and overall damage.
Research from Bridewell consultancy found that 69% of surveyed critical national infrastructure (CNI) organisations take up to six hours to respond to a ransomware attack, with nearly a third taking even longer. Experts argue this is far too slow.
Dray Agha, senior SOC manager at Huntress, suggests that failing to resolve a critical intrusion within 30 minutes presents a business risk. He cited an example where an attacker made significant, costly configuration changes within just 17 minutes.
"We have some cybercriminals that are able to essentially automate their malice when they get into an environment. So now, seconds matter... speed isn't just part of the solution, it's the entire solution."
He argues that a quick, imperfect initial response is often better than a delayed, perfect one.
The reliance solely on backups presents challenges:
- False Sense of Security: Backups might be outdated, incomplete, or untested. Disaster recovery plans might exist but haven't been practiced or are inaccessible if digital copies are encrypted.
- Competing Priorities: Business leaders often push for immediate restoration from backups to minimise downtime. However, security teams need time for forensic analysis to understand the root cause and ensure the threat is fully eradicated before restoring, as restoration can wipe crucial evidence.
- Restoration Doesn't Fix Everything: Simply restoring from backup doesn't address the initial vulnerability or remove attacker persistence if not properly investigated.
Effective IR requires investment in both tooling and skilled personnel. Agha stresses that security responsibilities cannot simply be added to existing IT staff; trained security operators are necessary. Continuous advocacy for security budgets, especially in SMBs and underfunded public sectors, is crucial. Until resources are fully adequate, prioritising rapid detection and response is key.
The difficult truth is that time is never on your side, and you'll have a hard time convincing any CEO that it was the right move to leave a known infection unremediated while you hunt for any other footholds - all while customer PII is siphoned or the attackers continue to inch closer to your crown jewels.
The final call-out is on the money - you need adequate skilled resources armed with the right tools, otherwise you have no choice but to put out fires as they come up and hope you'll outpace the attackers.
The Register | "30 minutes to pwn town: Are speedy responses more important than backups for recovery?"
Critical RCE Flaw Found in Apache Parquet

Heads up for anyone using Apache Parquet – a maximum severity (CVSS v4 10.0) Remote Code Execution (RCE) vulnerability, tracked as CVE-2025-30065, has been discovered. It affects all versions up to and including 1.15.0.
The vulnerability lies in the deserialisation of untrusted data within the parquet-avro module. An attacker could potentially exploit this by tricking a user or system into processing a specially crafted Parquet file. Successful exploitation could lead to arbitrary code execution, data theft or modification, service disruption, or even ransomware deployment.
Apache Parquet is a widely used open-source columnar storage format, popular in big data ecosystems like Hadoop, AWS, Azure, Google Cloud, and used by major companies such as Netflix, Uber, and LinkedIn.
The flaw was responsibly disclosed by Amazon researcher Keyi Li, and a fix is available in Apache Parquet version 1.15.1. Endor Labs suggests the issue might have been introduced in version 1.8.0 but advises checking all production stacks.
While exploitation requires convincing a target to import a malicious file, the potential impact is significant given Parquet's widespread use. Endor Labs warns:
"If an attacker tricks a vulnerable system into reading a specially crafted Parquet file, they could gain remote code execution (RCE) on that system."
If immediate patching isn't feasible, organisations are advised to avoid processing untrusted Parquet files, validate their safety carefully, and increase monitoring on systems handling Parquet data. No active exploitation has been reported yet, but upgrading to version 1.15.1 is strongly recommended.
Bleeping Computer | "Max severity RCE flaw discovered in widely used Apache Parquet"
'PoisonSeed' Phishing Campaign Targets Crypto Wallets via Marketing Platforms

Security researchers at SilentPush have identified a large-scale phishing campaign dubbed 'PoisonSeed'. This campaign compromises corporate accounts on popular email marketing platforms (like Mailchimp, SendGrid, HubSpot, Mailgun, Zoho) to distribute malicious emails targeting cryptocurrency users.
The attackers first identify and phish employees with access to these platforms using convincing fake login pages hosted on lookalike domains (e.g., mail-chimpservices[.]com). Once access is gained, they export mailing lists and generate API keys for persistent access.
Using the compromised marketing accounts, they send emails impersonating legitimate crypto platforms like Coinbase or Ledger. These emails often contain urgent alerts (e.g., "Coinbase is transitioning to self-custodial wallets") and include a pre-generated cryptocurrency wallet seed phrase. Users are instructed to import this seed phrase into a new wallet as part of a supposed migration or upgrade process.
The critical deception here is that the provided seed phrase is for a wallet already controlled by the attackers. If a victim imports this phrase and transfers their crypto assets into the associated wallet, the attackers can immediately drain the funds. This technique effectively "poisons" the user's attempt to create a secure wallet.
This campaign is linked to recent incidents involving compromised Mailchimp and SendGrid accounts used for Coinbase phishing. While sharing similarities with tactics used by groups like CryptoChameleon and Scattered Spider, SilentPush categorises PoisonSeed separately based on technical differences.
Bleeping Computer | "PoisonSeed phishing campaign behind emails with wallet seed phrases"
Europcar Suffers GitLab Breach, Customer Data Exposed

Car rental giant Europcar Mobility Group has confirmed a security breach involving its GitLab repositories. A threat actor gained access and exfiltrated source code for the company's Android and iOS applications, along with backups, cloud infrastructure details, internal application information, and some customer personal data.
The attacker, using the alias "Europcar," claimed to have obtained over 9,000 SQL backup files and 269 .env configuration files containing sensitive settings and credentials. They attempted to extort the company, threatening to release 37GB of stolen data. Screenshots of credentials found in the source code were published as proof.
Europcar confirmed the breach is real but stated that not all GitLab repositories were compromised. The investigation is ongoing, but the exposed customer data appears limited to names and email addresses belonging to users of its Goldcar and Ubeeqo brands. The number of affected customers is estimated to be between 50,000 and 200,000, potentially including data from as far back as 2017 and 2020. Europcar stated that more sensitive data like bank/card details and passwords were not exposed.
The company is notifying affected customers and relevant data protection authorities. The method used to gain access to the repositories is unclear, but infostealer malware compromising developer credentials is a common vector for such breaches.
Bleeping Computer | "Europcar GitLab breach exposes data of up to 200,000 customers"
Port of Seattle Notifies 90,000 After 2024 Rhysida Ransomware Attack

The Port of Seattle, the government agency managing Seattle's seaport and the Seattle-Tacoma (Sea-Tac) International Airport, is now formally notifying approximately 90,000 individuals whose personal information was compromised during a ransomware attack back in August 2024.
While the attack, attributed to the Rhysida ransomware group, caused significant IT outages, the Port confirmed that they refused to pay the ransom demanded, acknowledging that the attackers might consequently leak stolen data.
The investigation has now determined that personal information was indeed accessed and downloaded from legacy Port systems primarily containing employee, contractor, and parking data.
The compromised data varies by individual but may include:
- Names
- Dates of birth
- Social Security numbers (full or last four digits)
- Driver's license or other government ID numbers
- Some medical information
Rhysida ransomware emerged in May 2023 and has been linked to attacks on high-profile targets including the British Library, the Chilean Army, Insomniac Games, and MarineMax.
Bleeping Computer | "Port of Seattle says ransomware breach impacts 90,000 people"
The Record | "Port of Seattle says 90,000 people impacted in 2024 ransomware attack"
Pentagon Watchdog Probes Defense Secretary's Signal Use

The US Department of Defense's acting Inspector General (IG), Steven Stebbins, has launched an investigation into the use of the encrypted messaging app Signal by Defense Secretary Pete Hegseth for official government business.
This probe follows a request from Senators Roger Wicker (R-MS) and Jack Reed (D-RI), the ranking members of the Senate Armed Services Committee. Their concern stems from a report by The Atlantic's editor-in-chief, Jeffery Goldberg, who was accidentally added to a Signal group chat where Hegseth and other senior officials were discussing sensitive details about an upcoming airstrike in Yemen. The chat reportedly included targets, timing, and aircraft involved.
The senators raised concerns about the potential discussion of classified information on unclassified networks and the sharing of such information with individuals lacking proper clearance or need-to-know. The use of auto-deleting messages also raises questions about compliance with record-keeping requirements.
This investigation comes amidst reports that National Security Advisor Michael Waltz, who hosted the Signal group, also uses personal Gmail for government business and has set up numerous other government-related Signal groups.
The Register | "Signalgate: Pentagon watchdog probes Defense Sec Hegseth"
Russian Hacker Jailed for DDoS Attack on Domestic Tech Firm

A Russian court has sentenced a citizen from the Rostov region to two years in a penal colony for orchestrating a Distributed Denial-of-Service (DDoS) attack against a local technology company. The company was designated as part of Russia's critical information infrastructure.
According to Russia's Federal Security Service (FSB), the man organised the paid DDoS attack in April 2024. In addition to the prison sentence, he was fined 500,000 rubles (approx. $5,400). The FSB did not disclose who paid for the attack, but has previously accused Ukrainian intelligence of recruiting Russians for cyber campaigns within the country.
This conviction is part of a trend of increased reporting by Russian authorities of cases involving local citizens allegedly conducting cyberattacks against Russian interests or collaborating with foreign entities. Recent examples include arrests related to DDoS attacks during elections, alleged collaboration with Ukrainian intelligence for cyberattacks, and aiding Ukrainian hacker groups.
Meanwhile, legal proceedings against major Russian-linked cybercrime groups, such as the REvil ransomware gang members arrested over two years ago, appear to be progressing slowly, with defendants facing charges primarily related to illegal financial transactions rather than the hacking itself.
The Record | "Russia jails hacker for two years over cyberattack on local tech company"
Ex-ASML & NXP Employee Accused of Spying for Russia

A Russian national, identified only as German A., is facing industrial espionage charges in the Netherlands. He is accused of stealing semiconductor manufacturing secrets from his former employers, chip equipment giant ASML and semiconductor manufacturer NXP, and providing them to Russian intelligence services.
The Netherlands General Intelligence and Security Service (AIVD) alleges the man made multiple trips to Russia, meeting with intelligence operatives. He is accused of uploading sensitive information to Google Drive and carrying trade secrets into Russia on USB drives. He also allegedly contacted the Russian Innovative Engineering Center, an organisation focused on advancing chip technology.
The accused reportedly admitted possessing ASML documents but claimed it was for personal learning and that the files were outdated. He worked at electron-beam lithography startup Mapper from 2015 until it went bankrupt in 2020. ASML acquired Mapper and hired the accused, who is reportedly named on four ASML patents. However, his performance was deemed unsatisfactory, and he was laid off in 2021. He subsequently worked at NXP and later Delft University.
Dutch police arrested him in August 2024 following a tip from intelligence services. Confidential ASML documents and material related to Taiwanese chipmaker TSMC were allegedly found on his computer.
The Register | "Ex-ASML, NXP staffer accused of stealing chip secrets, peddling them to Moscow"