Daily News Update: Thursday, March 6, 2025 (Australia/Melbourne)

This post is an AI-generated summary of News Articles from a handful of publications over the last 24 hours. No credit is taken for the contents of said articles or the accuracy thereof.

Executive Summary
This summary covers various recent developments in cybersecurity, including the increasing speed of cyberattacks, notable ransomware incidents, and significant legal actions against cybercriminals. Key highlights include:
- Cybercriminal Efficiency: Cybercriminals are achieving lateral movement and data exfiltration faster than ever, with average breakout times dropping to 48 minutes.
- Ransomware Threats: Groups like Hunters International and Qilin are targeting large organizations, including Tata Technologies and healthcare facilities, with significant data theft demands.
- Chinese Cyber Activities: The U.S. has charged multiple Chinese nationals linked to extensive cyberattacks on government and private entities, emphasizing the ongoing threat from state-sponsored hacking.
- Emerging Threats: New botnets like Eleven11bot are infecting thousands of devices for DDoS attacks, while vulnerabilities in VMware products are being actively exploited.
- Legislative Developments: The U.S. Congress is considering expanding the cybersecurity role of the NTIA amid ongoing telecom attacks, highlighting the need for improved defenses.
Cybercriminals Increasingly Efficient in Attacks

Cybercriminals have significantly improved their attack speed, achieving lateral movement and data exfiltration at unprecedented rates. According to CrowdStrike, the average breakout time for lateral movement is now just 48 minutes, with some instances recorded as fast as 51 seconds. This trend indicates a worrying evolution in tactics, where attackers utilize legitimate system tools and automated processes to evade detection.
- Data Exfiltration: Palo Alto Networks reported that the median time from intrusion to data theft has decreased to about two days, with some cases taking less than an hour.
- Ransomware Dynamics: Ransomware attacks are becoming a race against time, with attackers rapidly escalating privileges and maintaining access for extended periods.
CyberScoop | "Cybercriminals picked up the pace on attacks last year"
Notable Ransomware Incidents

The ransomware group Hunters International has reportedly stolen 1.4 TB of data from Tata Technologies, threatening to leak sensitive information if their demands are not met. This incident underscores the ongoing risk to large organizations from sophisticated cybercriminals.
- Qilin Ransomware Attacks: The Qilin group has claimed responsibility for attacks on healthcare facilities, including a cancer clinic in Japan, where they stole 140 GB of sensitive patient data.
- Impact on Healthcare: These attacks highlight the vulnerabilities in the healthcare sector, where ransomware can disrupt critical services and endanger lives.
The Register | "Ransomware thugs threaten Tata Technologies with leak if demands not met"
The Register | "Qilin ransomware gang claims attacks on cancer clinic, OB-GYN facility"
Legal Actions Against Chinese Cybercriminals
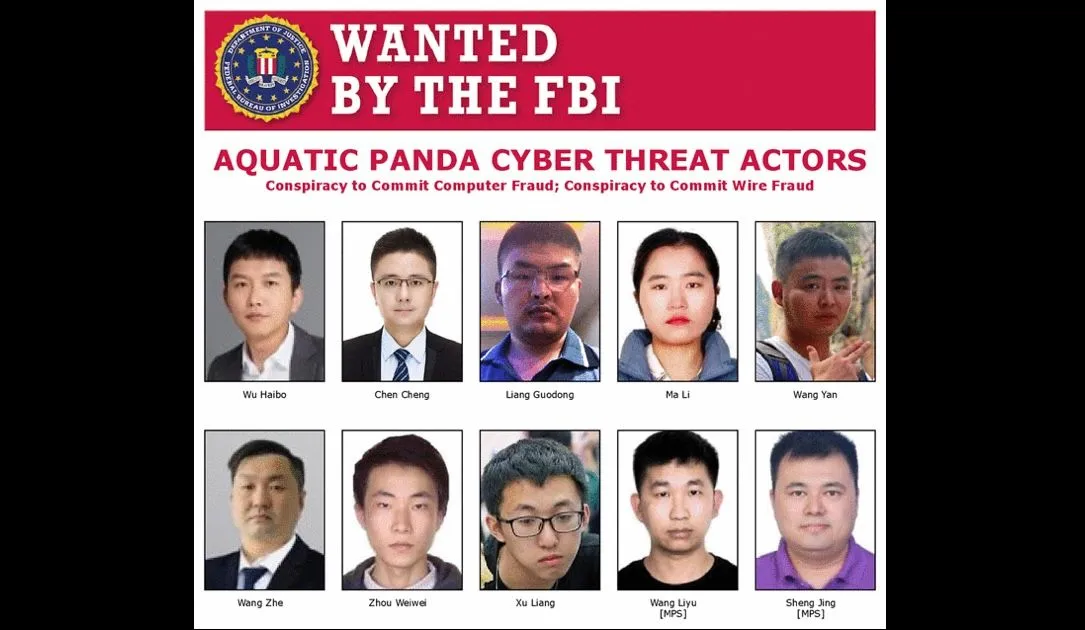
The U.S. Department of Justice has charged 12 Chinese nationals, including members of the Ministry of Public Security, for their involvement in extensive cyberattacks targeting U.S. government agencies and dissidents. This operation highlights the complex relationship between state-sponsored hackers and private firms in China.
- Charges and Indictments: The indictments reveal a systematic approach to cyber espionage, with hackers exploiting vulnerabilities to steal sensitive data and sell it to various Chinese government agencies.
- Ongoing Threats: The actions taken by the U.S. underscore the persistent threat posed by Chinese cyber activities, particularly against critical infrastructure and dissidents.
The Record | "US charges Chinese nationals in cyberattacks on Treasury, dissidents and more"
Emerging Cyber Threats and Vulnerabilities

Recent reports indicate the emergence of a new botnet, Eleven11bot, which has infected over 86,000 IoT devices for DDoS attacks. This botnet primarily targets security cameras and network video recorders, showcasing the vulnerabilities in IoT devices.
- VMware Vulnerabilities: The Cybersecurity and Infrastructure Security Agency (CISA) has warned about three critical vulnerabilities in VMware products that are currently being exploited.
- Legislative Response: In light of ongoing cyber threats, Congress is considering measures to enhance the cybersecurity role of the NTIA, particularly in response to attacks on telecommunications.
Bleeping Computer | "US charges Chinese hackers linked to critical infrastructure breaches"
Bleeping Computer | "New Eleven11bot botnet infects 86,000 devices for DDoS attacks"
Cybersecurity Needs in Rural Hospitals

A recent Microsoft report estimates that rural hospitals in the U.S. need to invest between $70 million and $75 million to address cybersecurity vulnerabilities. Many of these hospitals struggle to implement basic security measures, making them prime targets for ransomware attacks.
- Financial Constraints: The report highlights the financial difficulties faced by independent rural hospitals, which often lack the resources to enhance their cybersecurity posture.
- Impact of Cyberattacks: Ransomware attacks can severely disrupt patient care, posing life-threatening risks in isolated communities.
The Record | "Rural hospitals in US need to invest at least $70 million in cybersecurity, Microsoft finds"
Metadata
Cybersecurity, Ransomware, Cybercrime, Chinese Hackers, IoT Vulnerabilities, Rural Hospitals, Cyber Threats