Daily News Update: Tuesday, March 18, 2025 (Australia/Melbourne)

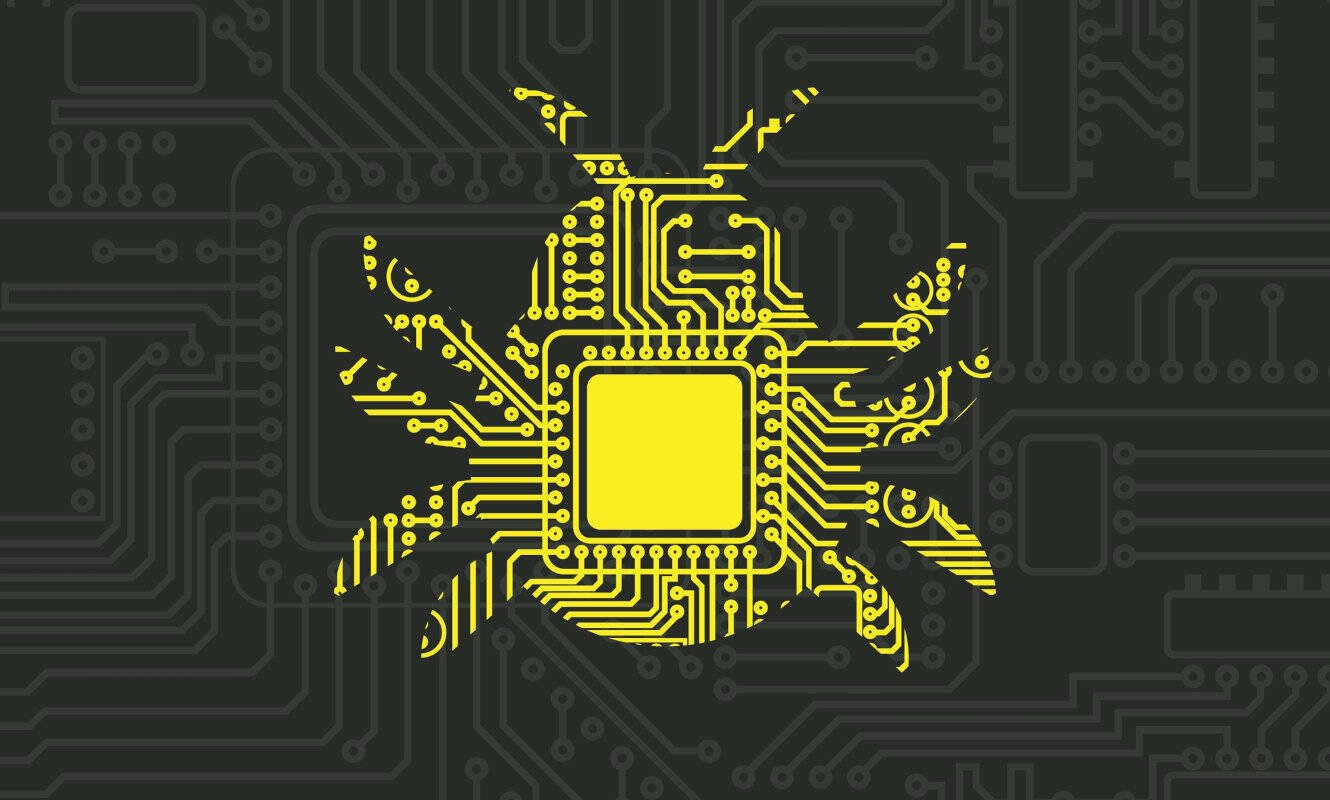
Tomcat RCE Vulnerability Under Attack

A critical remote code execution (RCE) vulnerability in Apache Tomcat, tracked as CVE-2025-24813, is being exploited in the wild. Attackers are using proof-of-concept (PoC) exploits - the first of which being posted just 30 hours after disclosure - to take over servers via a PUT request.
Wallarm security researchers confirmed the malicious activity, noting that traditional security tools struggle to detect it due to the expected receipt of PUT requests, in addition to the use of base64 encoding for the Java payload.
The vulnerability impacts Apache Tomcat versions 11.0.0-M1 to 11.0.2, 10.1.0-M1 to 10.1.34, and 9.0.0.M1 to 9.0.98. Apache recommends upgrading to versions 11.0.3+, 10.1.35+, or 9.0.99+ to mitigate the issue.
Bleeping Computer | "Critical RCE flaw in Apache Tomcat actively exploited in attacks"
BlackLock Ransomware Claims Nearly 50 Attacks
The ransomware-as-a-service (RaaS) operation 'BlackLock' has emerged as one of the more active ransomware operations of 2025, per CTI vendor DarkAtlas. Their research team identified BlackLock as a rebrand of Eldorado, a ransomware operation that emerged in March 2024. BlackLock uses a double-extortion model, stealing data and encrypting files.
DarkAtlas reports that the threat actors have performed 48 attacks on organizations across multiple sectors from January until February 2025.
BlackLock uses the same technical foundation as Eldorado: a Go-based cross-platform (Windows and Linux) ransomware using ChaCha20 for file encryption and RSA-OAEP for key encryption. Encrypted files are renamed with random filenames and file type extensions, and a ransom note titled "HOW_RETURN_YOUR_DATA.TXT" is created.
Dark Atlas | "BlackLock Ransomware: A Growing Threat Across Industries"
FCC Establishes Council on National Security

The United States Federal Communications Commission (FCC) is forming a Council on National Security to address foreign threats to American tech and telecommunications infrastructure. FCC chair Brendan Carr highlighted the persistent threat from foreign adversaries, particularly the Chinese Communist Party (CCP), aiming to breach networks and devices.
The Council's objectives are to counter these threats, though its collaboration with the Cybersecurity and Infrastructure Security Agency (CISA) is undefined. CISA's Cyber Safety Review Board previously investigated Chinese cyber threats, including the Salt Typhoon attacks, before being disbanded.
The Register | "FCC stands up Council on National Security to fight China in ways that CISA used to"
Microsoft's Bug Report Process Criticised
Will Dormann, a senior principal vulnerability analyst, criticised Microsoft Security Response Center (MSRC) for requiring a video proof-of-concept (POC) for a bug report, even with a clear description and screenshots.
Dormann created a 15-minute video featuring a screenshot from Zoolander and a techno backing track to comply maliciously with the request.
He argued that requiring a video signals that the reviewer is merely following a process rather than understanding the report. Dormann is still awaiting a response from Microsoft after submitting the video.
The Register | "Microsoft wouldn't look at a bug report without a video. Researcher maliciously complied"