SOC Goulash: Weekend Wrap-Up
13/02/2023 - 19/02/2023

This is an extended newsletter, so it may be truncated towards the end of the email. To read the full post, just select the View entire message hyperlink at the bottom of the email or Open in Browser!

Just how useful is “Cyber Incident” reporting?
Australian Critical Infrastructure providers have reported 47 “cyber incidents” between April and December last year, as mandated under the Security of Critical Infrastructure Act of 2018 (SOCI Act).
This Act was amended in 2022 to - among other things - provide the Australian government significant “step-in” powers that enable it to mandate changes to an operators network; require the provision of certain data, and intervene in the case of a significant cyber attack.
This drew concern from industry participants, and cemented the legislation as Australia’s most significant step taken to mitigate attacks on Critical Infrastructure to-date.
The Australian Cyber and Infrastructure Security Centre (CISC) first began accepting reports from April 1 last year, with it being made mandatory from July 8. The figures on the number of reports received were shared in a Senate Estimates hearing, though further details were not made available at the time.

What’s the significance?
While the number of reported cyber incidents may be eye-catching, it’s worth noting that a cyber security incident is defined somewhat broadly in the Act as the unauthorised access, modification or impairment of a computer, program, communications or data.
Given this definition, it’s unclear if this includes instances where - for example - a user unintentionally stumbles upon an open network share of another business unit. If such an instance meets the threshold for a reportable incident - the seriousness of these reports may well be negligent.
The specifics of these reports will almost certainly never be made public, so it remains to be seen if the mandatory reporting scheme legislated by the SOCI Act will actually provide the oversight that government agencies are hoping for, and how useful it will be in protecting Critical Infrastructure systems in the long-run.
In case you missed it…
GoDaddy discover years-old breach
An SEC filing by web hosting giant GoDaddy has revealed that it was the victim of a multi-year intrusion which saw attackers steal source code and lurk undetected on its servers, after initially breaching their cPanel shared hosting environment.
A press release issued by the company revealed that the investigation leading to this discovery began in December 2022, where customers complained that visitors to their websites were being intermittently redirected for no apparent reason. Investigators later discovered that their cPanel shared hosting environment had been compromised, and malware had been installed on customer websites to redirect victims to malicious websites.
The intrusion appears to be part of a larger campaign targeting hosting service providers, and GoDaddy claim they are working with “multiple law enforcement agencies around the world” to investigate the “sophisticated and organised group” behind the attacks.
Competence in Question
While GoDaddy has disclosed compromises in both March 2020 and November 2021 - these are believed to be linked to the multi-year campaign, and highlight the fact that the hosting provider seems to have failed to fully identify and eradicate the actor’s presence on more than one occassion.
If you’re a customer of GoDaddy, you’d be right to question how it took several years to uncover an actor lurking in a core piece of their infrastructure, and if you should trust them not to repeat their mistakes.
Opalsec is a reader-supported publication. To receive new posts and support my work, please consider becoming a paid subscriber!

Havoc C2 makes its debut
With Cobalt Strike well-known to Defenders, attackers have already begun experimenting with alternate C2 frameworks such as Brute Ratel, Sliver, and now - Havoc.
Like the others mentioned above, Havoc is an open-source, and highly capable C2 framework that utilises the familiar architecture of a Teamserver and Implants - referred to as “Demons” within the project.
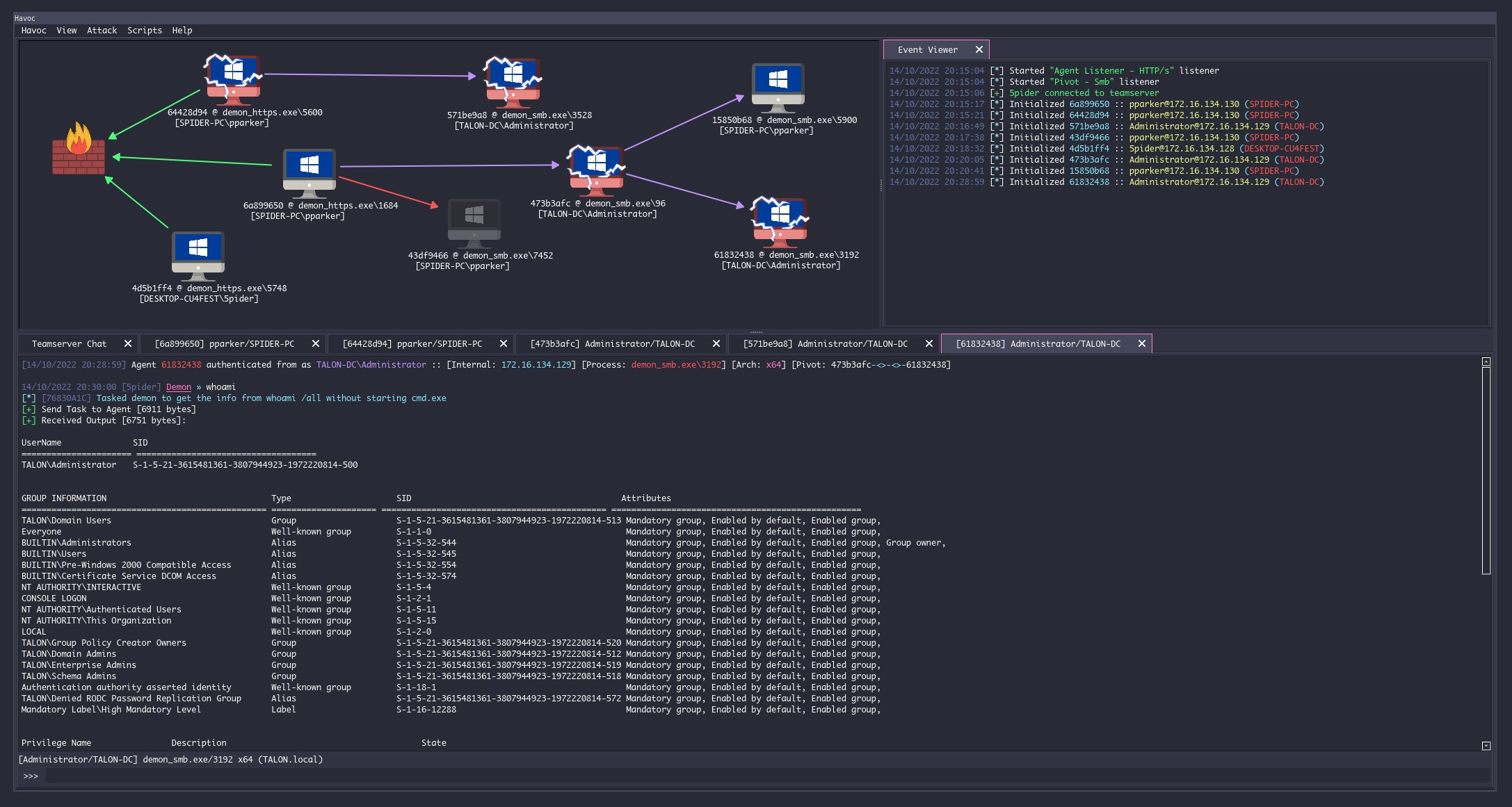
Researchers at Zscaler have published a report on an intrusion they responded to where the framework was seen deployed in a real-world attack - in this case targeting a Government organisation.
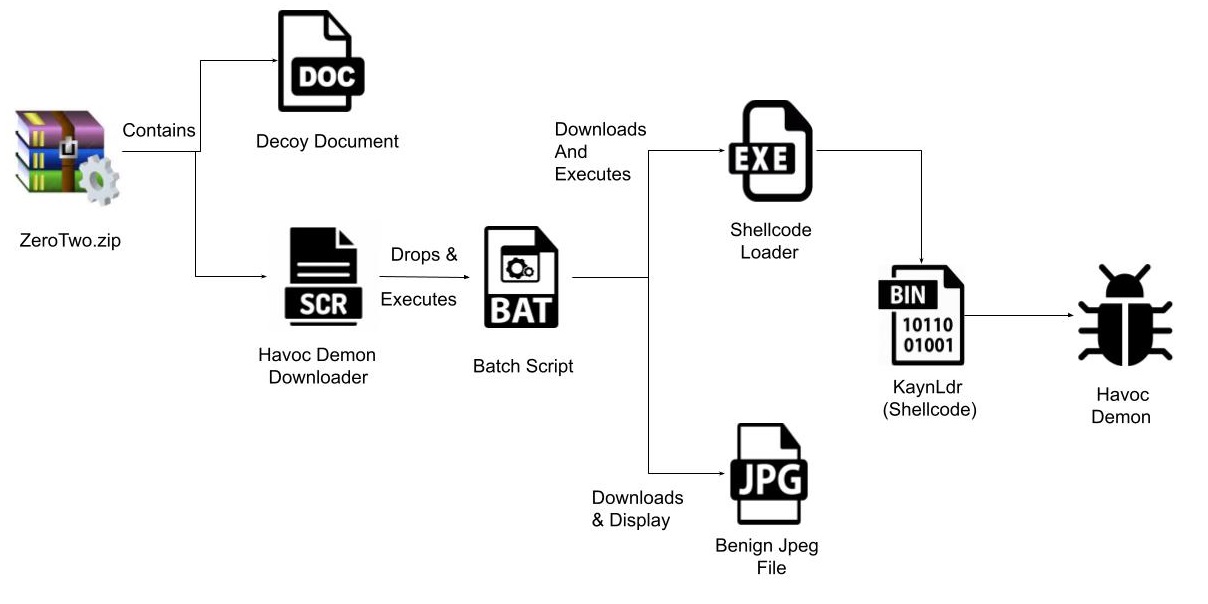
The initial, multi-staged delivery chain for the Havoc Demon used multiple decoy files, as well as a shellcode loader which is signed (invalid) by Microsoft’s Digital Signature to disable Event Tracing for Windows (ETW) in an attempt to neuter any EDR solutions running on the host.
A second piece of Shellcode dubbed “Kaynldr” then reflectively loaded the Havoc Demon DLL into memory and stripping the DOS and NT headers of the file - presumably to evade any string-based detections.
This campaign is noteworthy as it demonstrates that the C2 framework is operationally ready, and capable of integration with complex infection chains.
With Zscaler noting that it is sophisticated enough to bypass even “the most current and updated version of Windows 11 Defender” - the most commonly employed EDR agent in the market - we may yet see an uptick in real-world use of the Havoc framework, and must be prepared for it.
Frebniis - a novel, stealthy IIS backdoor
Researchers from Symantec have uncovered a new IIS backdoor deployed against targets in Taiwan (gosh, I wonder who could be behind this?), which it has dubbed “Frebniis”, after the abuse of IIS’ Failed Request Event Buffering feature.
Failed Request Event Buffering is a feature of IIS that’s meant to aid in troubleshooting of failed web page requests, but in this case the malware authors have repurposed it as a listener for incoming attacker tasking.
By hijacking a particular function pointer within the iisfreb.dll library, the attackers are able to inspect every HTTP request to the IIS server before returning to the original function, in order to ensure the feature continues to appear to work as expected.
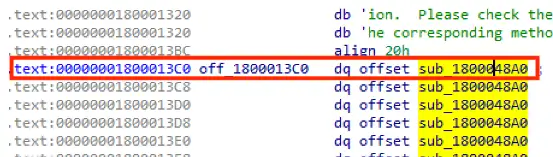
The backdoor is capable of enabling code execution by receiving, parsing and executing a base64-encoded string in-memory, and further acts as a proxy to internal systems that aren’t externally addressable.
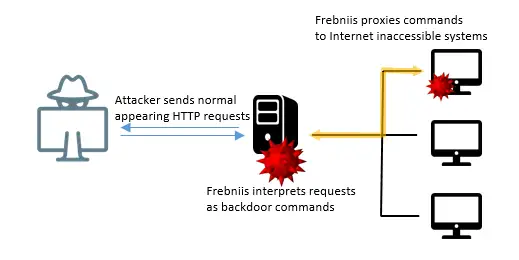
While IIS backdoors are nothing new, Frebniis is noteworthy for its novel abuse of the Failed Request Event Buffering feature, which allows it to avoid needing to import a malicious module - a technique that Defenders are familiar with, and will detect on.
Found this useful? Why not share it!
Other Reporting
- 🔥AhnLab analysts have reported on M2RAT - a new malware strain used by the North Korean APT37 group in a January phishing campaign that targeted South Korean entities. The malware is noteworthy as it scans for and pilfers documents from connected phones, and utilises shared memory to process commands an perform data exfiltration - leaving little evidence for forensicators to play with if they’re unable to get a live memory image for analysis;
- 🔥A SentinelLabs report on a new threat cluster tracked as WIP26 has unveiled a likely espionage-motivated campaign, in which they implemented both C2 and data exfil though trusted cloud service providers. Their implants leveraged m365 Mail and Google Firebase, while Azure and Dropbox instances were used to facilitate data exfil and payload staging;
- Censys have continued monitoring the spread of ESXiArgs ransomware, and good news - the number of infected hosts appears to have dropped by nearly 300 since the start of last week. Further analysis by their researchers has uncovered early victims from as far back as October last year;
- 🔥eSentire have published a report looking at Icarus Stealer - a cheap, Malware-as-a-Service infostealer which is unique in its use of hVNC to spawn a hidden virtual desktop which it uses to navigate the victim system;
- Analysis by Group-IB has established links between the SideWinder, Baby Elephant, and Donot APT groups through analysis of a widespread spearphishing campaign targeting Central and South Asian countries in the second half of 2021. The likely Indian, espionage-motivated group was found to have a more geographically dispersed set of infrastructure and numerous additional malware families than previously thought;
- SentinelOne researchers have determined that the TZW ransomware strain discovered by analysts at AhnLab is in fact a rebrand of the GlobeImposter/LOLKEK ransomware group, which has been around since 2016 and tracked under multiple monikers;
- 🔥Researcher German Fernandez has picked up what looks to be a single Threat Actor distributing both Qakbot and IcedID malware using the same decoy document and server. This doesn’t look to be any of the typical IcedID (TA551) or Qakbot (TA570, TA577) distributors, and is a neat illustration of the affiliate-based cyber crime ecosystem at work;
- Checkpoint’s January leaderboard has Qakbot, Lokibot, and AgentTesla taking top spots in malware distribution, while they also highlight Vidar stealer’s return to the top 10 after a widespread “brandjacking” campaign which spread the malware via fake AnyDesk installers;
- Beep is a new infostealing malware comprised of a dropper, injector and payload, though is most notable for the obscene lengths it goes to in order to evade detection & analysis. The malware is still being developed and only in limited use in-the-wild, but has basic capabilities and is likely one to keep an eye on;
- AT&T have shared a short write-up on the GuLoader malware, summarising the malware’s infection chain, evasive measures, and use in real-world attacks;
- NCC Group have published a detailed technical analysis of the Hydra Android banking trojan and the infrastructure used in its campaigns;
- Cisco Talos has flagged a Phishing campaign that spreads both ransomware and a crypto-jacking malware on victim systems. The ransomware - dubbed MortalKombat - appears to be a modified version of the leaked Xorist ransomware builder which itself is over 10 years old.
Critical bugs patched in Fortinet kit
Fortinet has released patches for its FortiNAC and FortiWeb products to address two critical vulnerabilities that it uncovered - potentially as early as October 2021.
CVE-2022-39952 impacts FortiNAC appliances and could potentially allow for unauthenticated, arbitrary file write on a vulnerable system to execute code, earning it a CVSS score of 9.8.
The FortiWeb WAF, on the other hand, is impacted by a buffer overflow vulnerability (CVE-2021-42756) that could enable arbitrary code execution via a crafted HTTP request, and has a CVSS rating of 9.3.
Opalsec is a reader-supported publication. To receive new posts and support my work, please consider becoming a paid subscriber!
Patches for actively exploited vulnerability in Apple devices
Emergency patches were released earlier last week in response to a zero-day, arbitrary code execution vulnerability (CVE-2023-23529) discovered to impact Apple’s iPhone, iPad, and Mac devices.
The exploit stems from a flaw in the WebKit browser engine, and while it was flagged as being actively exploited by Apple, no further details were shared as to who was targeted or by whom.
This vulnerability can be exploited by simply presenting victims a maliciously crafted page, and impacts Apple devices as far back as the iPhone 8. Get your skates on and make sure you’re patched - even CISA says so!
CISA urges patching of four Citrix vulns
Citrix has unveiled patches for four high-severity vulnerabilities affecting their Virtual Apps, Desktops, and Workspace Apps products, with impacts ranging from session takeover to privilege escalation.
While the vulnerabilities are not remotely exploitable, the most serious of the four is still significant as it would allow an attacker to elevate to SYSTEM privileges and achieve full control over the compromised host.
Once again, CISA have called these vulnerabilities out and urged administrators to apply the patches as soon as possible.

Offensive
- 🔥OffensivePipeline - A tool that can help randomise values in cloned offensive projects before build time - obfuscating the resulting binary and generating shellcode;
- 🔥NimPlant - A lightweight implant written in Nim and Python, tailored for first-stage delivery;
- Lepus - A (self-appointed) fast tool for enumerating subdomains, checking for subdomain takeovers and performing port scans;
- Andy Robbins from SpecterOps has shared a great write-up looking at the potential to abuse Azure Managed Identities to elevate to Global Admin;
- Did you know that - by default - users can create Azure subscriptions within their tenant, which even the tenant Global Admin won’t be able to see? I’m guessing there are at least a few Azure admins out there that don’t 🙃;
- This is a handy guide on how to set up mr.d0x’s noVNC phishing technique using AWS;
- Check out this write-up on a straightforward Okta MFA bypass technique, though as the post notes at the start - this is a post-exploit technique requiring admin privileges;
- Another Red Team Cheatsheet to add to your list - this one helpfully lists the command line arguments you keep forgetting, as well as some Opsec tips that will help evade the Blue Team.
Defensive
- 🔥Threat Intel juggernaut Recorded Future has published an exhaustive paper that looks at trends in attacks on VMWare’s ESXi platform, including recommendations for how to secure it; exploit it, and detect those exploit attempts;
- Microsoft Defender for Identity has been updated to detect suspicious certificate usage (i.e. ADCS abuse) - check out this post that illustrates an example attack scenario that it can mitigate against;
- Kostas Tsale has begun toying with the idea of Sigma for Threat Hunting, and while he’s waiting to see if the official Sigma is interested in supporting it, you can check out a sample of a proposed rule here;
- 🔥Speaking of Threat Hunting, Stephan Berger has shared a great thread which highlights two useful Hunt hypotheses extracted from an article by AON, that will help Defenders surface attacks that leverage the evilginx2 phishing kit;
- Yoroi have published a post that follows-up on Unit42’s analysis of a real-world campaign that abused the Brute Ratel framework, highlighting that many samples are still going fully or mostly undetected by AVs represented in VirusTotal;
- BOFs (Beacon Object Files) are a integral part of the Cobalt Strike framework, but isn’t something Defenders are typically familiar with. If you’re keen to learn, TrustedSec have you covered.
- For anyone who celebrated the demise of the Blender cryptocurrency mixer following its sanctioning by the US - it’s time to pop that cork back in the champagne. Researchers at Elliptic have found it “highly likely” that the service was relaunched as early as October last year under the name Sinbad, and has already been used by the Lazarus group to launder nearly $100 million in Bitcoin;
- Cloudflare have claimed top spot for having mitigated the largest volumetric DDoS on record, which hit over 71 million requests per second - more than 54% higher than the previous record set in June 2022;
- Researchers found they were able to hijack an npm package with over 3.5 million weekly downloads by re-registering a lapsed domain which the original author had used an email address from to register the project in npm;
- Zscaler have shared their 2022 Cloud (In)Security Report, which highlights worrying stats on the number of organisations with significant misconfigurations and a lack of MFA for privileged access, for example.
Opalsec is a reader-supported publication. To receive new posts and support my work, please consider becoming a paid subscriber!